 Supports macOS Sequoia Learn More
Supports macOS Sequoia Learn More
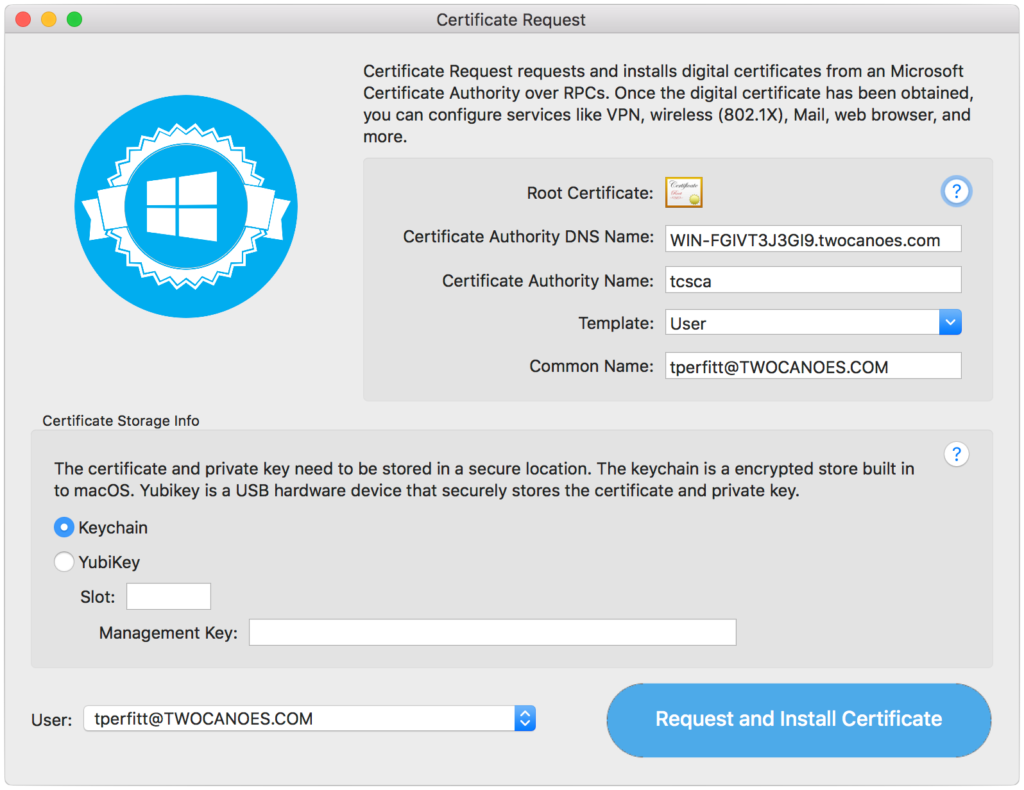
Certificate Request
Get Digital Certificates for macOS from Active Directory Natively
BuyTry Certificate Request for 14 Days!
Fill out this form to download your 14-day trial with a license key. You will receive an email with links to download the software.
Certificate Request from Twocanoes Software
Certificate Request is a powerful utility for the Mac that allows you to request and install digital certificates directly from Active Directory. This utility automatically discovers all the required information from Active Directory, once you have obtained a kerberos ticket; then, requesting a digital certificate can be as simple as clicking a single button. The digital certificate can be used for configuring wireless, Mail, VPN, and many other services on macOS that require certificates issued by Active Directory.

Native Requests
Certificate Request doesn’t require any changes to Active Directory. Certificate requests are sent over standard Windows protocols (DCE/RPC).
Active Directory binding not required
Certificate Request uses Kerberos to authenticate with Active Directory and doesn’t require the Mac to be bound to Active Directory. If the Mac is bound, Certificate Request can use the existing kerberos credentials from login to request a certificate.
Smart
Certificate Request automatically discovers all of the Active Directory information that is required, including the name of the Active Directory Certificate Authority server, the Certificate Authority name, and all available certificate templates. Certificate Request downloads the Active Directory Root Certificate automatically and makes it easy to configure the Mac to trust it.
Keychain or YubiKey
Certificate Request installs digital certificates directly to the standard macOS keychain or YubiKey hardware encryption device. The private key never leaves the keychain or the YubiKey, so it is secure.
Advanced Authentication
Certificate Request automatically detects if a login has already occurred and if there are kerberos credentials available. If there are multiple credentials available, Certificate Request gives the option to select the appropriate one; Certificate Request can also purge all credentials. Certificates use SHA512 hashing and 2048 bit RSA keys.
Multiple Template Support
Since digital certificates can be used in many different services, Active Directory bundles the settings into Templates. Certificate Request shows all available templates on the Active Directory server and makes it easy to select the appropriate one for the service you require (e.g., VPN, Mail, Wi-Fi, etc).
Simple, Yet Powerful
When Certificate Request is first launched, all the necessary Active Directory information needed to request a user certificate is automatically populated. Certificate Request is simple and easy to use with your existing Active Directory infrastructure without making any changes.
Intensely Integrated
Certificate Request doesn’t require a proxy or web services to work with your existing Active Directory network. DCE/RPC, a protocol that Windows Servers understand natively, is used to send all certificate requests.
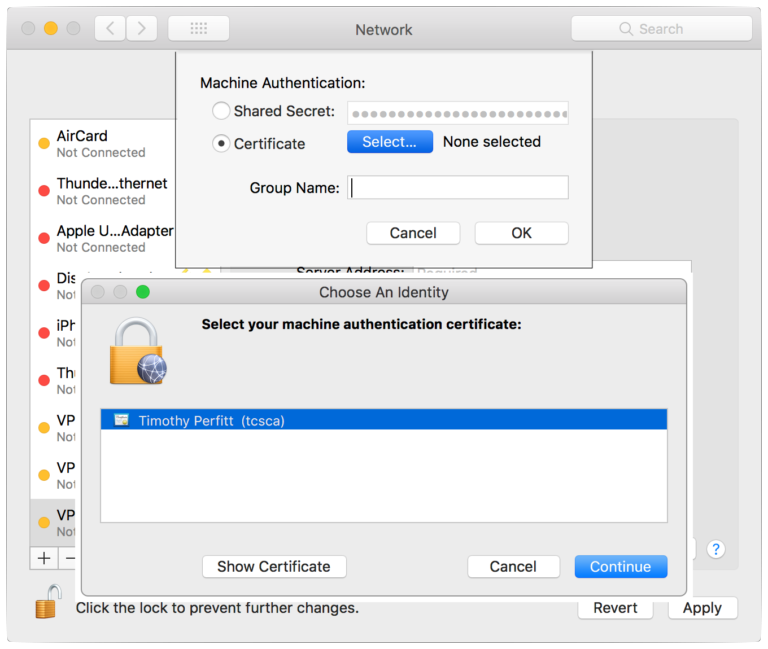
At Your Service
Configure any services that require digital certificates easily. Certificate Request stores the digital certificate in the secure keychain on macOS, or in a YubiKey hardware device, so services such as VPN, Mail, 802.1X (wireless), and more can easily access them.
Automate
The Certificate Request command line tool allows administrators to automate certificate requests to Active Directory and installation into the keychain on macOS. The command line tool uses the user’s kerberos credentials so that certificate generation can happen seamlessly.
Certificate Request Requirements and Specs
System Requirements
macOS
macOS 14 Sonoma or 15 Sequoia
Active Directory user credentials for a kerberos ticket, or a Mac bound to Active Directory
Windows Server
Active Directory (Windows Server 2003 or later)
Standard Network Ports for LDAP, RPC, and Kerberos
YubiKey
YubiKey 4 Series Security Keys in PIV mode
Management Key
Available Slot for digital identity
Technical Specs
Version history
Generates X.509 Digital Certificates
SHA512 Hash
RSA 2048 bit keys
Kerberos Authentication
Keep In Touch
Sign Up for Certificate Request security and product updates




